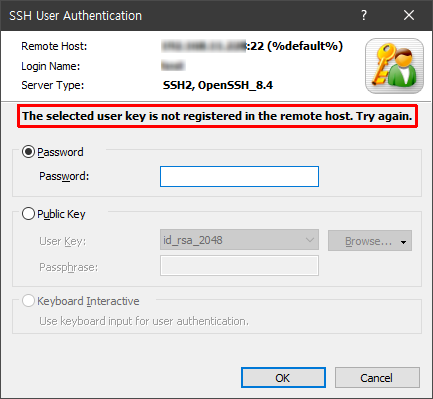
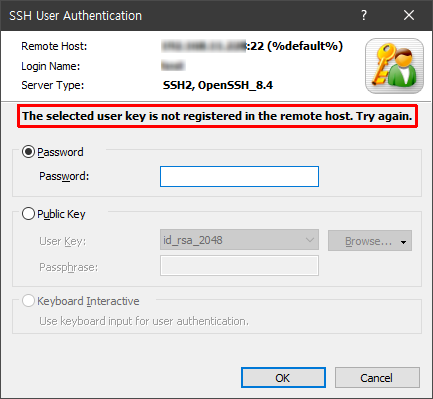
Connecting to 123.123.123.123:22... Connection established. To escape to local shell, press Ctrl+Alt+]. [14:47:16] Version exchange initiated... [14:47:16] server: SSH-2.0-OpenSSH_8.4 [14:47:16] client: SSH-2.0-nsssh2_7.0.0006 NetSarang Computer, Inc. [14:47:16] SSH2 is selected. [14:47:16] Outgoing packet: 20 (0x14: SSH2_MSG_KEXINIT) [14:47:16] Incoming packet: 20 (0x14: SSH2_MSG_KEXINIT) [14:47:16] Algorithm negotiation initiated... (Dialog mode) [14:47:16] key exchange: curve25519-sha256@libssh.org [14:47:16] host key: rsa-sha2-256 [14:47:16] outgoing encryption: chacha20-poly1305@openssh.com [14:47:16] incoming encryption: chacha20-poly1305@openssh.com [14:47:16] outgoing mac: hmac-sha2-256-etm@openssh.com [14:47:16] incoming mac: hmac-sha2-256-etm@openssh.com [14:47:16] outgoing compression: none [14:47:16] incoming compression: none [14:47:16] Outgoing packet: 30 (0x1e: SSH2_MSG_KEXDH_INIT) [14:47:16] Incoming packet: 31 (0x1f: SSH2_MSG_KEXDH_REPLY) [14:47:16] Host authentication initiated... [14:47:16] Hostkey fingerprint: [14:47:16] rsa 3072 8a:c3:90:89:16:7a:43:ad:db:ca:d5:7d:91:c0:7e:c1 [14:47:16] Accepted. Verifying host key... [14:47:16] Verified. [14:47:16] Outgoing packet: 21 (0x15: SSH2_MSG_NEWKEYS) [14:47:16] Incoming packet: 21 (0x15: SSH2_MSG_NEWKEYS) [14:47:16] Outgoing packet: 5 (0x05: SSH2_MSG_SERVICE_REQUEST) [14:47:16] Incoming packet: 6 (0x06: SSH2_MSG_SERVICE_ACCEPT) [14:47:16] User authentication initiated... (Dialog mode) [14:47:17] Sent user name 'testuser'. [14:47:17] Outgoing packet: 50 (0x32: SSH2_MSG_USERAUTH_REQUEST) [14:47:17] Incoming packet: 51 (0x33: SSH2_MSG_USERAUTH_FAILURE) [14:47:23] Outgoing packet: 50 (0x32: SSH2_MSG_USERAUTH_REQUEST) [14:47:23] Sent public key blob, type:ssh-rsa. [14:47:23] Incoming packet: 51 (0x33: SSH2_MSG_USERAUTH_FAILURE) [14:47:23] Server rejected the public blob. |
This issue occurred because the SSH server does not accept the Xshell supported ssh-rsa key format(SHA1).
When OpenSSH 8.2 was released, OpenSSH stated that the ssh-rsa key format would be excluded from the default list in the near future.
(https://www.openssh.com/txt/release-8.2)
Fedora 33, released in October 2020, includes OpenSSH 8.4 by default, and the ssh-rsa format is omitted from the default list in its OpenSSH server as expected.
You can choose one of the followings:
Change the crypto-policy on Fedora 33 and restart the SSH server.
# update-crypto-policies --show; update-crypto-policies --set LEGACY; systemctl restart sshd |
Add the ssh-rsa format to the SSH server configuration file. (Note: This is not recommended for security reasons.)
Add 'PubkeyAcceptedKeyTypes +ssh-rsa' before the 'Include'
# vi /etc/ssh/sshd_config |
... PubkeyAcceptedKeyTypes +ssh-rsa ... # To modify the system-wide sshd configuration, create a *.conf file under # /etc/ssh/sshd_config.d/ which will be automatically included below Include /etc/ssh/sshd_config.d/*.conf ... |
# systemctl restart sshd |