(If you only want the quick step-by-steps, scroll down to Basic Step-by-Step Guide near the bottom of this article)
For public key authentication the public user key must be registered on the server you want to connect to and also to the user. This approach can be considered inefficient, and it can also be a burden to the server administrator. Thus, using a public key authenticated via a Certificate Authority (CA) can be a superior solution. OpenSSH provides simple certificate generation and an associated CA infrastructure. Xshell can utilize OpenSSH CAs to connect to remote UNIX/Linux servers. The following guide will show how you can use the CA feature of OpenSSH in Xshell.
If you use an authenticated key, even if the SSH server's host key changes, if the corresponding host key is signed, the key will be recognized as the host key of the same server in the SSH client. This is useful if you need to make frequent changes to the host key. Also, it grants the server administrator the ability to set and manage expiration dates of private keys as well as the ability to revoke private keys used by users outright. Users can connect to the server only with public keys authenticated by the authentication server.
IMPORTANT: To use this feature in Version 6, the OpenSSH Certificate Authority option must be enabled in Help => Experimental Features.
Run the following command on the certificate creation server. Create a password when prompted. You will need to enter this password to authenticate the key later.
$ ssh-keygen -f server_ca Generating public/private rsa key pair. Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in server_ca. Your public key has been saved in server_ca.pub. The key fingerprint is: SHA256:wkoynUi5rXkMQXcNrpFmOWh+JbONIOCxeWv8WOxUbm4 root@uby The key's randomart image is: +---[RSA 2048]----+ |... . oo | |o.++ = . | |.+B.X o. | | =oXo&o | | B+X++oS | | .X*.o. | | o.+o E | | . . | | | +----[SHA256]-----+ |
In our example, we created an rsa server_ca key to be used for authentication. If you'd like to use a non-rsa formatted key, use the -t option to specify the desired key format.
Confirm that the authentication key pair has been created.
$ ls |
If the host key to be signed is not from the authentication server, use the scp command to bring the host key from the appropriate server. Keep in mind that only root has read access to the SSH server host key.
Get the remote server's host key to be signed②:
# scp root@host.netsarang.com:/etc/ssh/ssh_host_rsa_key.pub . |
Use the Signing Key to sign the host key:
# ssh-keygen -s server_ca -I key_id -h -n host.netsarang.com -V +52w ssh_host_rsa_key.pub |
Option Explanations
s: Name of the Signing Key.
I: Name used for logging purposes.
h: Indicates that what you are signing is a host key.
n: Name of the SSH server that will use the Signing Host Key. You can use commas to list multiple servers. SSH clients must utilize one of these names. If this value is omitted, then you can use it on any SSH server.
V: Certificate validity period. The example above has specified 52 weeks (1 year).
Copy the signed host key of the remote server to the applicable remote server③. The location in which it's saved must be specified in the sshd_config:
# scp ssh_host_rsa_key-cert.pub root@host.netsarang.com:/etc/ssh/ |
Once the steps above are completed, the host key and the authenticated host key which were copied over are no longer needed. You can delete them:
# rm ssh_host_rsa_key.pub ssh_host_rsa_key-cert.pub |
Edit the following file on the SSH server. You must have root privileges:
# vi /etc/ssh/sshd_config |
Locate the HostCertificate line (if it does not exist, create it) and enter the name of the signed host key created in the step above④. An authenticated host key file is a host key file which was first authenticated on an authentication server and then copied over.
HostCertificate /etc/ssh/ssh_host_rsa_key-cert.pub |
After saving, use the following command to restart the SSH Daemon.
# service ssh restart |
Copy the contents of the authentication file Signing Public Key (server_ca.pub) from the authentication server.
# cat ~/server_ca.pub |
Add the above copied contents to the ca_keys file⑤. Now, add @cert-authority and domain restriction information in front of the public key information and then save the file.
@cert-authority *.netsarang.com ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQCxC+gikReZlWEnZhKkGzhcNeRD3dKh0L1opw4/LQJcUPfRj07E3am |
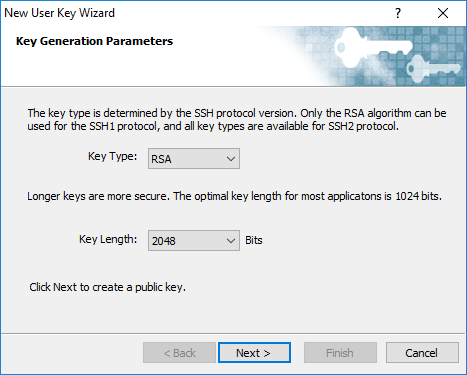
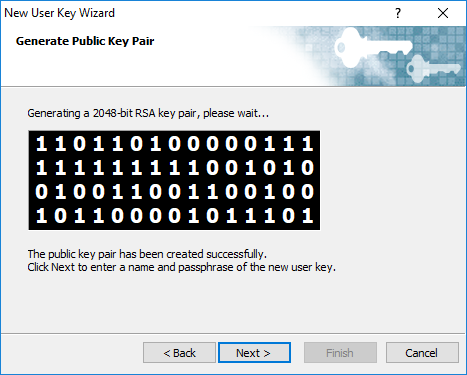
In order to sign the user keys in the authentication server, we need to first create a Signing Key set:
# ssh-keygen -f users_ca |
Create a password when prompted. You will need this password when using this key to sign other keys.
In our example, we created an rsa server_ca key to be used for authentication. If you'd like to use a non-rsa formatted key, use the -t option to specify the desired key format.
From the Signing Key set we created in the authentication server above, copy the public key to the SSH server②. You must have root privileges for the SSH server.
# scp users_ca.pub root@host.netsarang.com:/etc/ssh/ |
In the SSH server, modify the SSH daemon config file, sshd_config. You must have root privileges:
# vi /etc/ssh/sshd_config |
Add the following information under the HostCertificate line that you applied during host authentication③. The users_ca.pub file is the file you copied over in Step 1.
TrustedUserCAKeys /etc/ssh/users_ca.pub |
Restart the SSH service daemon.
# service ssh restart |
Use the users_ca file to sign the key. The process is similar to signing a host key, but since this is a user key, you won't use the -h parameter. In the command below, the "username1,username2" after the -n parameter are SSH server's usernames. You can list the usernames you want to use when connecting with the signed key. Unlike the host key signing process, if you leave this value blank, you will not be able to login as any user on the SSH server with the above user keys. This value must be specified.
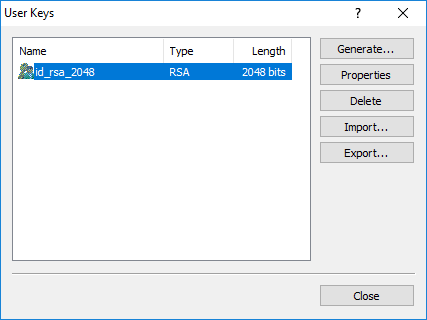
$ ssh-keygen -s users_ca -I key_id -n username1,username2,... -V +52w id_rsa_2048.pub |
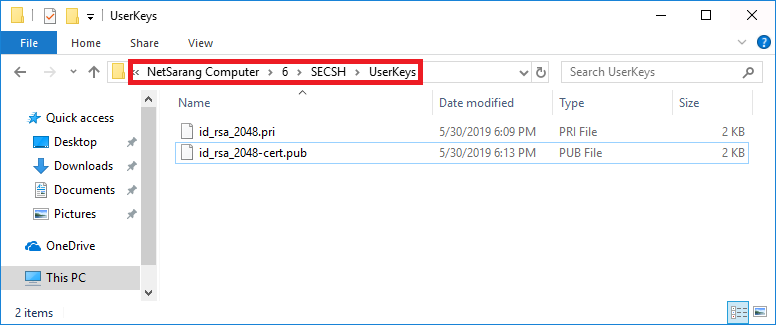
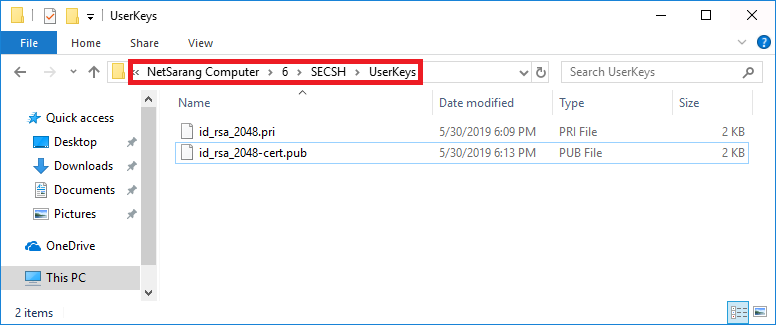
When prompted to enter the password, enter the password you created when creating the users_ca file. Confirm that a signed file, id_rsa_2048-cert.pub, has been created.
Confirm
Confirm that the user you want logging into the SSH server does not have public key information:
$ hostname |
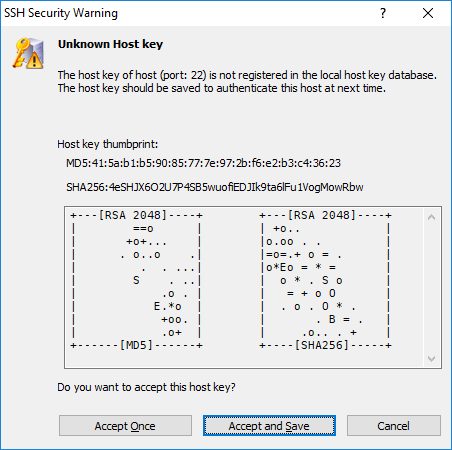
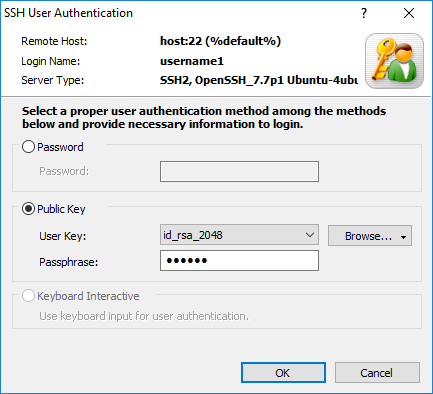
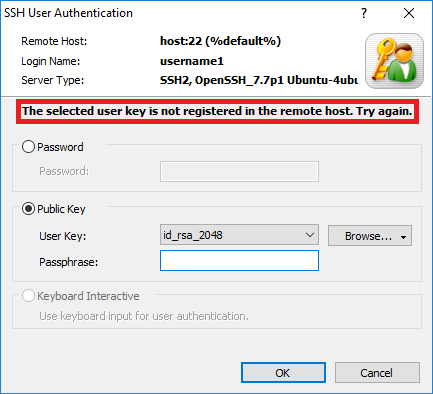
From Xshell, make an SSH connection to the SSH server. 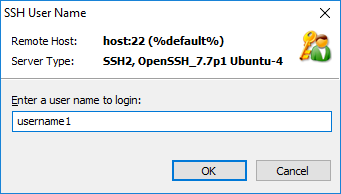
If the user key is not authenticated, you will see:
If the user key is authenticated:
Even if the public key was not registered on the SSH server, you can still login by entering the key password of the SSH client's private key (id_rsa_2048). Connections made by the users (username1,username2,...) entered after the -n parameter when signing the public key can login without registering the public key.
Create the Signing Key in the CA server①
$ ssh-keygen -f server_ca |
Transfer the SSH server's host key to be signed to the CA server②:
# scp root@host.netsarang.com:/etc/ssh/ssh_host_rsa_key.pub . |
Use in the Signing Key in the CA server to sign the host key:
# ssh-keygen -s server_ca -I key_id -h -n host.netsarang.com -V +52w ssh_host_rsa_key.pub |
Copy the signed host key of the remote server to the applicable remote server③:
# scp ssh_host_rsa_key-cert.pub root@centy.netsarang.com:/etc/ssh/ |
Specify the signed host key in the sshd_config's HostCertificate line④:
HostCertificate /etc/ssh/ssh_host_rsa_key-cert.pub |
After saving, use the following command to restart the SSH Daemon.
# service ssh restart |
Copy the contents of the authentication file Signing Public Key (server_ca.pub) from the authentication server and paste it into the ca_keys file⑤. Now, add @cert-authority and domain restriction information in front of the public key information and then save the file.
@cert-authority *.netsarang.com ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQCxC+gikReZlWEnZhKkGzhcNeRD3dKh0L1opw4/LQJcUPfRj07E3ambJ |
*Create the Signing Key①:*
# ssh-keygen -f users_ca |
From the Signing Key set we created in the authentication server above, copy the public key to the SSH server②:
# scp users_ca.pub root@host.netsarang.com:/etc/ssh/ |
In the SSH server, modify the SSH daemon config file, sshd_config. Specify the users_ca.pub file for TrustedUserCAKeys:
TrustedUserCAKeys /etc/ssh/users_ca.pub |
Restart the SSH service daemon:
# service ssh restart |
Use the users_ca file to sign the key.
$ ssh-keygen -s users_ca -I key_id -n username1,username2,... -V +52w id_rsa_2048.pub |